Edward Snowden’s Permanent Record
John Walker
[email protected]
Special to L. Neil Smith’s The Libertarian Enterprise
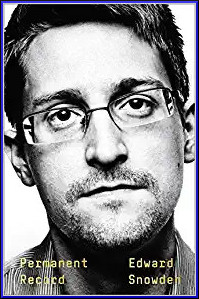
Permanent Record
by Edward Snowden
New York: Metropolitan Books, 2019.
ISBN 978-1-250-23723-1.
The revolution in communication and computing technologies which has continually accelerated since the introduction of integrated circuits in the 1960s and has since given rise to the Internet, ubiquitous mobile telephony, vast data centres with formidable processing and storage capacity, and technologies such as natural language text processing, voice recognition, and image analysis, has created the potential, for the first time in human history, of mass surveillance to a degree unimagined even in dystopian fiction such as George Orwell’s 1984 or attempted by the secret police of totalitarian regimes like the Soviet Union, Nazi Germany, or North Korea. But, residents of enlightened developed countries such as the United States thought, they were protected, by legal safeguards such as the Fourth Amendment to the U.S. Constitution, from having their government deploy such forbidding tools against its own citizens. Certainly, there was awareness, from disclosures such as those in James Bamford’s 1982 book The Puzzle Palace, that agencies such as the National Security Agency (NSA) were employing advanced and highly secret technologies to spy upon foreign governments and their agents who might attempt to harm the United States and its citizens, but their activities were circumscribed by a legal framework which strictly limited the scope of their domestic activities.
Well, that’s what most people believed until the courageous acts by Edward Snowden, a senior technical contractor working for the NSA, revealed, in 2013, multiple programs of indiscriminate mass surveillance directed against, well, everybody in the world, U.S. citizens most definitely included. The NSA had developed and deployed a large array of hardware and software tools whose mission was essentially to capture all the communications and personal data of everybody in the world, scan it for items of interest, and store it forever where it could be accessed in future investigations. Data were collected through a multitude of means: monitoring traffic across the Internet, collecting mobile phone call and location data (estimated at five billion records per day in 2013), spidering data from Web sites, breaking vulnerable encryption technologies, working with “corporate partners” to snoop data passing through their facilities, and fusing this vast and varied data with query tools such as XKEYSCORE, which might be thought of as a Google search engine built by people who from the outset proclaimed, “Heck yes, we’re evil!”
How did Edward Snowden, over his career a contractor employee for companies including BAE Systems, Dell Computer, and Booz Allen Hamilton, and a government employee of the CIA, obtain access to such carefully guarded secrets? What motivated him to disclose this information to the media? How did he spirit the information out of the famously security-obsessed NSA and get it into the hands of the media? And what were the consequences of his actions? All of these questions are answered in this beautifully written, relentlessly candid, passionately argued, and technologically insightful book by the person who, more than anyone else, is responsible for revealing the malignant ambition of the government of the United States and its accomplices in the Five Eyes (Australia, Canada, New Zealand, and the United Kingdom) to implement and deploy a global panopticon which would shrink the scope of privacy of individuals to essentially zero—in the words of an NSA PowerPoint (of course) presentation from 2011, “Sniff It All, Know It All, Collect It All, Process It All, Exploit It All, Partner It All”. They didn’t mention “Store It All Forever”, but with the construction of the US$1.5 billion Utah Data Center which consumes 65 megawatts of electricity, it’s pretty clear that’s what they’re doing.
Edward Snowden was born in 1983 and grew up along with the personal computer revolution. His first contact with computers was when his father brought home a Commodore 64, on which father and son would play many games. Later, just seven years old, his father introduced him to programming on a computer at the Coast Guard base where he worked, and, a few years later, when the family had moved to the Maryland suburbs of Washington DC after his father had been transferred to Coast Guard Headquarters, the family got a Compaq 486 PC clone which opened the world of programming and exploration of online groups and the nascent World Wide Web via the narrow pipe of a dial-up connection to America Online. In those golden days of the 1990s, the Internet was mostly created by individuals for individuals, and you could have any identity, or as many identities as you wished, inventing and discarding them as you explored the world and yourself. This was ideal for a youth who wasn’t interested in sports and tended to be reserved in the presence of others. He explored the many corners of the Internet and, like so many with the talent for understanding complex systems, learned to deduce the rules governing systems and explore ways of using them to his own ends. Bob Bickford defines a hacker as “Any person who derives joy from discovering ways to circumvent limitations.” Hacking is not criminal, and it has nothing to do with computers. As his life progressed, Snowden would learn how to hack school, the job market, and eventually the oppressive surveillance state.
By September 2001, Snowden was working for an independent Web site developer operating out of her house on the grounds of Fort Meade, Maryland, the home of the NSA (for whom, coincidentally, his mother worked in a support capacity). After the attacks on the World Trade Center and Pentagon, he decided, in his family’s long tradition of service to their country (his grandfather is a Rear Admiral in the Coast Guard, and ancestors fought in the Revolution, Civil War, and both world wars), that his talents would be better put to use in the intelligence community. His lack of a four year college degree would usually be a bar to such employment, but the terrorist attacks changed all the rules, and military veterans were being given a fast track into such jobs, so, after exploring his options, Snowden enlisted in the Army, under a special program called 18 X-Ray, which would send qualifying recruits directly into Special Forces training after completing their basic training.
His military career was to prove short. During a training exercise, he took a fall in the forest which fractured the tibia bone in both legs and was advised he would never be able to qualify for Special Forces. Given the option of serving out his time in a desk job or taking immediate “administrative separation” (in which he would waive the government’s liability for the injury), he opted for the latter. Finally, after a circuitous process, he was hired by a government contractor and received the exclusive Top Secret/Sensitive Compartmented Information security clearance which qualified him to work at the CIA.
A few words are in order about contractors at government agencies. In some media accounts of the Snowden disclosures, he has been dismissed as “just a contractor”, but in the present-day U.S. government where nothing is as it seems and much of everything is a scam, in fact many of the people working in the most sensitive capacities in the intelligence community are contractors supplied by the big “beltway bandit” firms which have sprung up like mushrooms around the federal swamp. You see, agencies operate under strict limits on the number of pure government (civil service) employees they can hire and, of course, government employment is almost always forever. But, if they pay a contractor to supply a body to do precisely the same job, on site, they can pay the contractor from operating funds and bypass the entire civil service mechanism and limits and, further, they’re free to cut jobs any time they wish and to get rid of people and request a replacement from the contractor without going through the arduous process of laying off or firing a “govvy”. In all of Snowden’s jobs, the blue badged civil servants worked alongside the green badge contractors without distinction in job function. Contractors would rarely ever visit the premises of their nominal “employers” except for formalities of hiring and employee benefits. One of Snowden’s co-workers said “contracting was the third biggest scam in Washington after the income tax and Congress.”
His work at the CIA was in system administration, and he rapidly learned that regardless of classification levels, compartmentalisation, and need to know, the person in a modern organisation who knows everything, or at least has the ability to find out if interested, is the system administrator. In order to keep a system running, ensure the integrity of the data stored on it, restore backups when hardware, software, or user errors cause things to be lost, and the myriad other tasks that comprise the work of a “sysadmin”, you have to have privileges to access pretty much everything in the system. You might not be able to see things on other systems, but the ones under your control are an open book. The only safeguard employers have over rogue administrators is monitoring of their actions, and this is often laughably poor, especially as bosses often lack the computer savvy of the administrators who work for them.
After nine months on the job, an opening came up for a CIA civil servant job in overseas technical support. Attracted to travel and exotic postings abroad, Snowden turned in his green badge for a blue one and after a training program, was sent to exotic…Geneva as computer security technician, under diplomatic cover. As placid as it may seem, Geneva was on the cutting edge of CIA spying technology, with the United Nations, numerous international agencies, and private banks all prime targets for snooping.
Two years later Snowden was a contractor once again, this time with Dell Computer, who placed him with the NSA, first in Japan, then back in Maryland, and eventually in Hawaii as lead technologist of the Office of Information Sharing, where he developed a system called “Heartbeat” which allowed all of NSA’s sites around the world to share their local information with others. It can be thought of as an automated blog aggregator for Top Secret information. This provided him personal access to just about everything the NSA was up to, world-wide. And he found what he read profoundly disturbing and dismaying.
Once he became aware of the scope of mass surveillance, he transferred to another job in Hawaii which would allow him to personally verify its power by gaining access to XKEYSCORE. His worst fears were confirmed, and he began to patiently, with great caution, and using all of his insider’s knowledge, prepare to bring the archives he had spirited out from the Heartbeat system to the attention of the public via respected media who would understand the need to redact any material which might, for example, put agents in the field at risk. He discusses why, based upon his personal experience and that of others, he decided the whistleblower approach within the chain of command was not feasible: the unconstitutional surveillance he had discovered had been approved at the highest levels of government—there was nobody who could stop it who had not already approved it.
The narrative then follows preparing for departure, securing the data for travel, taking a leave of absence from work, travelling to Hong Kong, and arranging to meet the journalists he had chosen for the disclosure. There is a good deal of useful tradecraft information in this narrative for anybody with secrets to guard. Then, after the stories began to break in June, 2013, the tale of his harrowing escape from the long reach of Uncle Sam is recounted. Popular media accounts of Snowden “defecting to Russia” are untrue. He had planned to seek asylum in Ecuador, and had obtained a laissez-passer from the Ecuadoran consul and arranged to travel to Quito from Hong Kong via Moscow, Havana, and Caracas, as that was the only routing which did not pass through U.S. airspace or involve stops in countries with extradition treaties with the U.S. Upon arrival in Moscow, he discovered that his U.S. passport had been revoked while en route from Hong Kong, and without a valid passport he could neither board an onward flight nor leave the airport. He ended up trapped in the Moscow airport for forty days while twenty-seven countries folded to U.S. pressure and denied him political asylum. After spending so long in the airport he even became tired of eating at the Burger King there, on August 1st, 2013 Russia granted him temporary asylum. At this writing, he is still in Moscow, having been joined in 2017 by Lindsay Mills, the love of his life he left behind in Hawaii in 2013, and who is now his wife.
This is very much a personal narrative, and you will get an excellent sense for who Edward Snowden is and why he chose to do what he did. The first thing that struck me is that he really knows his stuff. Some of the press coverage presented him as a kind of low-level contractor systems nerd, but he was principal architect of EPICSHELTER, NSA’s worldwide backup and archiving system, and sole developer of the Heartbeat aggregation system for reports from sites around the globe. At the time he left to make his disclosures, his salary was US$120,000 per year, hardly the pay of a humble programmer. His descriptions of technologies and systems in the book are comprehensive and flawless. He comes across as motivated entirely by outrage at the NSA’s flouting of the constitutional protections supposed to be afforded U.S. citizens and its abuses in implementing mass surveillance, sanctioned at the highest levels of government across two administrations from different political parties. He did not seek money for his disclosures, and did not offer them to foreign governments. He took care to erase all media containing the documents he removed from the NSA before embarking on his trip from Hong Kong, and when approached upon landing in Moscow by agents from the Russian FSB (intelligence service) with what was obviously a recruitment pitch, he immediately cut it off, saying,
Listen, I understand who you are, and what this is. Please let me be clear that I have no intention to cooperate with you. I’m not going to cooperate with any intelligence service. I mean no disrespect, but this isn’t going to be that kind of meeting. If you want to search my bag, it’s right here. But I promise you, there’s nothing in it that can help you.
And that was that.
Edward Snowden could have kept quiet, done his job, collected his handsome salary, continued to live in a Hawaiian paradise, and share his life with Lindsay, but he threw it all away on a matter of principle and duty to his fellow citizens and the Constitution he had sworn to defend when taking the oath upon joining the Army and the CIA. On the basis of the law, he is doubtless guilty of the three federal crimes with which he has been charged, sufficient to lock him up for as many as thirty years should the U.S. lay its hands on him. But he believes he did the correct thing in an attempt to right wrongs which were intolerable. I agree, and can only admire his courage. If anybody is deserving of a Presidential pardon, it is Edward Snowden.
There is relatively little discussion here of the actual content of the documents which were disclosed and the surveillance programs they revealed. For full details, visit the Snowden Surveillance Archive, which has copies of all of the documents which have been disclosed by the media to date. U.S. government employees and contractors should read the warning on the site before viewing this material.
Reprinted from Fourmilog: None Dare Call It Reason John Walker’s web site for September 23, 2019.
Was that worth reading?
Then why not:
![]()
|
Support this online magazine with
|
AFFILIATE/ADVERTISEMENT
This site may receive compensation if a product is purchased
through one of our partner or affiliate referral links. You
already know that, of course, but this is part of the FTC Disclosure
Policy
found here. (Warning: this is a 2,359,896-byte 53-page PDF file!)
